

Windows Server OSes running CrowdStrike affected too


Windows Server OSes running CrowdStrike affected too


This VPN protocol usually uses a private key (client) / public key (server) combo that is used to connect through a public IP address (the 2 nodes can’t communicate it without) using the specified TCP or UDP (more often lately) and port to create the VPN tunnel that’s gets established during the handshakes.
There is a whole lot more going on with the process but that’s a high level view. But I have a WireGuard VPN service running on a raspberry pi that I put in a DMZ on my perimeter firewall.
But a port scanner would be able to see that port is open. Make sure you keep your software up to date. Hopefully the software devs of the VPN application is keeping their stuff up to date to avoid any vulnerabilities getting exposed in the code and a backdoor getting created because of it. As long as that doesn’t become an issue, no one will be able to get through without the private key. And those are usually uncrackable in a lifetime with the complexity and length of the key.
So I’m a VMware Horizon Customer / Engineer - I have a specific set of VMware Instant Clone VDIs that I created for a bunch of sales managers for the company I work for. They all use the iPad Pro 12.9s and they love them. They still need access to their green screen and spread sheets from a Windows VDI, so that’s what they have.
From what they report the experience is great. Make sure to use a keyboard with it and a Bluetooth mouse with it. Trust me, it’s worth it.


We do: Firefox, Chrome, or Edge. That’s not the problem.
The problem is with Microsofts new driver we can’t allow users to set the default browser in their VMware Instant Clone using SetUserFTA via Dynamic Environment Manager.


We have 80,000 people that work for my company. That’s not going to happen. Now we have 10,000 VMs running a combination of Ubuntu, Red Hat, Debian, and Centos. But our employees choose the OS they want to run on their own work devices whether it be Linux, MacOS, or Windows and no way is everyone is going to Linux, even if that is my own OS of choice. Especially the C-Level and board member types.


We are using Instant Clones. It’s a non-persistent Virtual Desktop.
We want to give our users the choice and then be able to persist those choices. Not force them to use just one option with a GPO that defines what they have to use.
SetUserFTA and Dynamic Environment Manager allowed it until the last Windows CU came along…


This is horrible. I run several different environments of VMware Instant Clone VDIs and use the SetUserFTA to help a users default browser and other file extension defaults to persist for a user from session to session on a non-persistent VDI. Now it’s broken.
Thanks a lot Microsoft. 😤


deleted by creator


Talk less and listen more.
Realize that there is always someone that knows more than you do about any subject. Be humble knowing that you can always learn more.


Tempting to short the stock and say $&@# you Spez!


Glad I could help! 😃


Ok, I grabbed a few screen shots for you as well. Here is a site that will link you to MEBx setup that enables AMT: http://h10032.www1.hp.com/ctg/Manual/c03883429
When power on your ProDesk G3, you can access the MEBx setup by pressing Ctrl+P or they also say F6 or Escape will get you there. Intel AMT runs on a different IP address than what your OS gets. You can assign DHCP or a static IP address and setup your admin password. You can then access the portal from http://ipaddress:16992 There should be a method of access what would show on the screen through a KVM like access but I use MeshCentral for that so I couldn’t tell you how to do it without.
Hopefully, that gives you a start. Feel free to reach back out if you have any questions. Thank you!
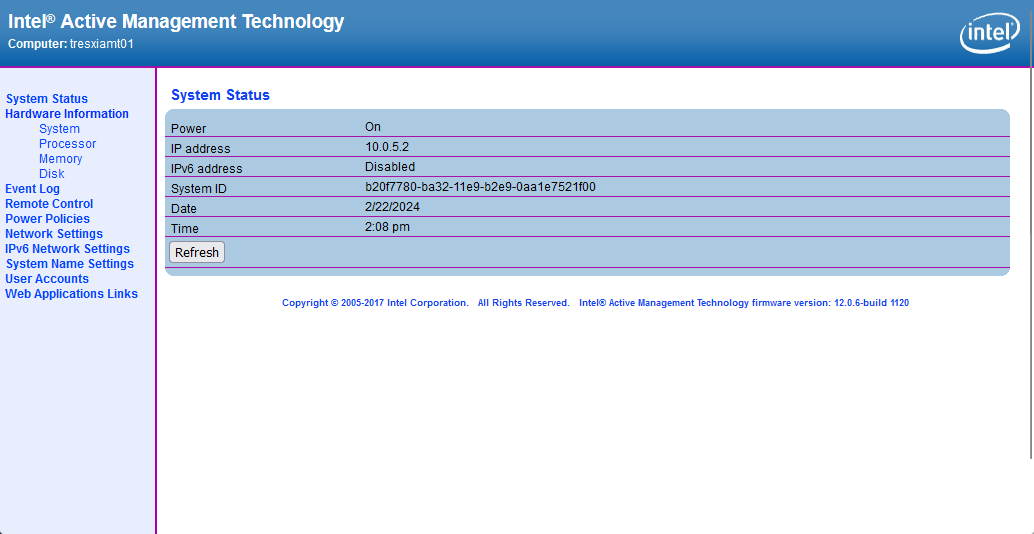



I’m not in front of my computer atm, but I think I have something that can help you out. I have a 3-node Lenovo Thin client cluster that I manage their KVMs using the Intel vPro. I even went a step further using MeshCentral running on a VM to centralize my KVM access since I have 3 of them, but that’s another story.
Anyway, I’ll see if I can grab you some URLs in the morning if someone else doesn’t beat me to it or you find it on your own running google queries.


Ok, so looking at the BSOD minidumps, the BSOD from 2/13/24 and 1/10/2024 give a bug check event that is typically driver related. My recommendation would be to download prime95 and use the “Blend” test for a couple of hours to try and recreate the BSOD. If you don’t get anything you can try running 3DMark to force it. It’s easier when you can “recreate” the problem on purpose instead of waiting for it to happen. Once you reproduce the BSOD you can try and go through the Event Log and determine which driver was the cause since there will be an Application Error usually present.
If you can’t find anything in the logs, you can always pull out all peripherals and use prime95 for another couple of hours making sure that the issue is gone. If you still get a BSOD, you’ve got other hardware causing the issue. (or you could have a combination of both)
If you can’t reproduce the BSOD after unplugging the peripherals, plug one back in at a time stress testing to determine which peripheral is causing it. But you should be able to find it in the event log. I hope this helps.


I should be able to take a look tomorrow morning. I had a similar issue with an Intel Raptor Lake build. So I’ll let you know what I did to narrow it down.


2024 - Mexicans at the border (you know it’s already happening)


There is a BSOD viewer by Nirsoft that is free located here: https://www.nirsoft.net/utils/blue_screen_view.html
This will allow you to take a look at the dump files that were created with each BSOD and typically give you the file name that typically is involved. Can you get that information and let us know what it gives you. This will give you a better idea of what the cause is.


3-Node ESXi cluster with 10 Debian VMs, 3 Windows VMs, and one FreeBSD VM


Examples: ServiceNow, Connectwise, Jira Service Desk
No it has not. Validated on Ubuntu 16.04, 18.04, 20.04, 22.04 running CrowdStrike Sensor